Let's Talk About Pentesting
Hey folks!
So now you’ve learned a little bit about incident response but now you’re like well thanks James, but what goes through an attackers mindset? That gets us to Penetration Testing!! Uhhhh what? Penetration Testing…What does that mean James? I know I know without context of the cybers you’re confused, it’s ok. Low brow jokes aside, Pen Testing or Penetration Testing is the name for the field of ethical hacking where “hackers” or pentesters will receive permission from a client, to attack their stuff. For the purpose of seeing what information the pentester (simulating an attacker) can gather, what privileges they can obtain, etc. Seems interesting right? Now Pentesting, just like Incident Response is a massive field with a lot of different niches and specialties. That being said let’s talk about the Pentesting Lifecycle or the 6 Phases of a Pentest. Just like in the last post we’re going to stick to using an amalgamation of popular takes on the cycle.
Let’s get to it!
- Phase 1: Pre-Engagement Interactions
- This is the part where you need to get permission before you do anything. The client will either come to you or you to them. The main goal during this phase is to begin to draw up the paper work. The logistics of the engagement, expectations, scope, legal implications, goals and objectives that the client wants to achieve with your pentest.
- The number one most essential thing you will ever need in a pentest is a get out of jail free card: a document that states you’re authorized to be doing what you are doing, that you’ve been given permission and you can’t legally become implicated, so long as you stick to your scope of the pentest, and follow the rules outlined in the legal paperwork. You keep that card/paper safe. Make copies of it. Put it in your pocket. Put it in your other pocket. Leave one at your Mom’s house!
- Some details you will wanna specify with the client are things like whether or not they want the pentest to simulate an external threat like an outside attacker trying to get in, or an internal threat like an employee that’s mad and tries to get company data out.
- You wanna be careful to develop definitions, and specifics, the more details the better, as you really want to create a gauge for how aggressive the client wants you to become.
- Phase 2: OSINT && Reconnaissance
-
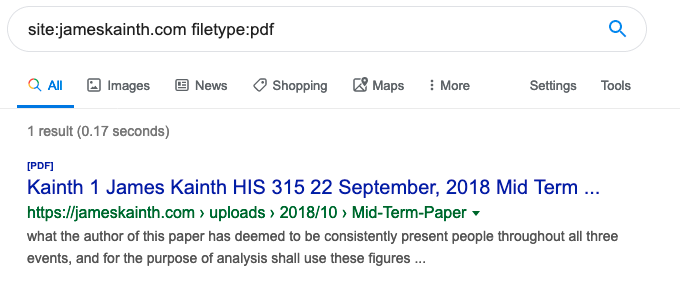
This is where the fun begins!!! ( ͡° ͜ʖ ͡°) We get to start working on Open Source INTelligence (OSINT) this is literally just scraping the public webz for information that can be useful. You’d be surprised the amount of information people leave hanging out on the public facing internet where anyone can access it. I’ve found crazy things!! Financial documents, Private publications, and obviously tons and tons of PII (Personally Identifiable Information). I mean we’re all guilty of it! Hell I’m sitting here with my damn face plastered on this site, the domain is literally James Kainth so like, it doesn’t get any easier than that. What happens is you can start to build a portfolio of your targets. There’s so many fun things in this phase already, we gotta use OSINT so using tools like Metagoofil, TheHarvester, Maltego, Recon-Ng, Shodan, and alike to scrape the web. You can even use the classic command line tools like “nslookup” to use DNS(the magic that turns an IP 127.0.0.1 into a domain home.com using pointer records, etc. more on DNS to come 🙂
-
This is where even more fun comes in too, so OSINT has two stages. Passive, where you don’t touch the client at all you’re using an intermediate source, think talking to your friend about a girl you like: you’re getting information about the girl from your friend who knows about her, that way your crush doesn’t know you wanna hangout and watch romantic comedies with her. Even better you think of it like asking your friend for college recommendations and you read (note that I didn’t say scan) their website, the college hasn’t a clue you’re learning about them.
-
The Active part of OSINT is when you don’t care so much about touching the client sites(obviously don’t go tipping them off running like a -T5 nmap scan lol). You start to scan their website their IPs/Subnets to see what ports are open, what types of software they’re running, what’s the network look like (you design a network diagram), and whatever helpful information you can gather without actually engaging the client yet(think: we’re still looking at the building but not going in.) You can use Netcraft to build reports on certain websites for example.
-
Basically there’s so much fun to be had just by google dorking(“advanced” google searching for files on domains etc.) and falling down research rabbit holes to build a profile on the target. And at this point you’re not even really doing anything crazy you’re just looking at information publicly available. Literally like if YOU yes YOU want to find information you can.
-
-
Phase 3: Planning Exploits and Threat Modeling
-
Yes I know the bullet point changed…I wanted to put the pic in there and still keep the formatting but I couldn’t… thanks WordPress 😒 I’ll probably switch to a Jekyll site when I get the chance at some point, idk. Ok quick break over. 😐 🙄😐 (lolol told y’all i’d update…a year later here we are 😉 consistent bullets yay!)
-
This is like taking the fun from before and turning it up a level. Before you were turnt, now you’re lit!!!
-
This is where you start to find exploits using sites like exploit-db, metasploit, googling etc. When you have a list of software versions you have a list of potential entry points. If you’re using Windows 7 and haven’t patched to the latest security update you’ll get exploited. That’s why security updates are so important. Whenever a new vulnerability is released the developers will patch it and that’s when you’re safer (note I didn’t say safe £spoiler you’re never safe in cyberspace £OnlyTheParanoidSurvive wuddup Harold Finch[mah GOALS] wuddup Andrew Grove[legend]) You can run Nessus Scans for vulnerability detection (maybe I’ll make a post about Nessus hmmm 🤔 I did just work at Tenable shoutout … 😛 😛 +XP )
-
You should have a list of IPs by now to the best of your ability and a report detailing some common areas to map further: Employee Data, Customer Data, Technical Data, Company Secrets, Where Jon Snow was going in the last episode of GoT (lookin at you HBO lookin at you)
-
Think of threats YOU as an attacker will face:
- external threats like physical security, locks, security guards, ID scanners, other employees, etc.
- internal threats like a firewall, IDS (Intrusion Detection System), IPS (Intrusion Prevention System), a SIEM (Security Information and Event Manager)[aka the reason why I truly believe there’s no way to get away with a crime…those electrons are gonna be left behind somewhere shout out to the Man from the East ], etc.
-
-
Phase 4: Engagement & Exploitation The “real” Pen Test
-
So this is where you take those exploits you’ve gathered and try em out. Most often then not you’ll be able to successfully exploit a system unless the version is up to date and the client is patched to which case you should be happy, they’re “secure”, or you can build your own custom exploits (I’m not that leet but maybe you are, idk, looking at you BinaryZone[you know who you are 😉 ya legend])
-
So you get in right, then you gotta see if you can get lateral movement. Can you move around the network? Can you move from box to box? Or are you stuck in a subnet(a different network segment on a network)? Can you exploit some more? Do some more scanning(be strategic about that you don’t want anyone knowing you’re there)
-
As you’re on the network you gotta be doing all the stuff from before that I talked about. Recon, but this time you’re doing it almost on the fly cause you may come across something that you didn’t know existed or something you didn’t expect. You gotta be adaptable. Blend into your surrounding the best you can.
-
This would also be a good reminder for me to remind the pen tester to stay in scope. Remember you’re only allowed to do so much, and target certain things. That get out of jail card won’t work if you’re getting sent to Alcatraz, Iron Heights, Blackgate Penitentiary, Arkham Asylum, or the like.
-
Pause, take a deep breath there’s a lot to take in I know, this is a load of information and it can be scary. That’s because it is. Pentesting is a form of Ethical Hacking but like Yin and Yang there’s the bad guy who does this just to wreak havoc, but there’s also the good guys. Deep breathes. Don’t forget my fellow DF/IR fam 😉 our bois in Blue(and women too, errybodyyy 😛 )
-
Ok cool, this is where we get to not just the digital exploitation and privilege escalation. But this is where we go from being lit, to the James clouds of OMFG I CANNOT BELIEVE I’M DOING THIS RIGHT NOW! These levels of fun are literally where you’re shaking. Out of fear. That’s how much fun you’re having. I’m talking about Social Engineering! My friends hear me say this term a lot (it’s a real life skill, what can I say, you do it everyday too, to your boss, or your professors, you want a raise/recognition at work? you want a better grade?) Social Engineering is when you take advantage of a potential victim’s natural tendencies and emotional reactions. There’s the extremes of social engineering than there’s the basics. Social engineering can go so far as being described as flat out manipulation of people, to giving you what you want. Whether it be a raise, or confidential information.
-
Social Engineering can happen to you face to face as in I can be doing it to you right now 😈, someone can be sending you a phishing email, or it can even be that IT guy you never met but who said “he works help desk downstairs” when in reality IT is on the 5th floor and you’re on the 6th level.
-
So I know all this sounds scary and it is. Like there’s legitimate cause for concern but there’s ways for you to prevent those attacks from happening( for the sake of this post I won’t get into it but I’ll add it to the docket)
-
Once you have access to wherever you have access you also want to make sure you have persistence, install a backdoor or someway for you to be able to get right back to where you were with much more ease.
-
Once you’re in, another thing to do is to cover your @$$. You really should’ve been doing this as you went along tbh, but lol if you weren’t thinking about it already lmao you weren’t ready in the first place. £CyberSass Remember when I talked about SIEMS, so they log everything (assuming they’re configured correctly, if not then haha more power to us) What you want to do is hide in plain site, so if you’re going to download a backdoor, you’d want to name it as a service that looks real. You don’t want to have the user looking at their task manager window and seeing PentesterHere.exe. It’s funny actually quick story: when I was younger like 12 years old I had a MacBook(Thanks Mom and Dad for supporting me in all the ridiculicious Jamesventures young and old) and I was learning how to make small apps using Apple Script… is that still a thing?…But I would make an app on my computer that would do something as stupid as pop up in a window that would say “This is not what you think it is” with a close button to exit out. The thing about that though was that Apple has that get info properties feature and I could copy and paste an image to make the app look like whatever I wanted. So I would remove the Safari icon from the Dock (the list of common apps) and put my program there with the icon as the Safari logo. I would troll people cause I didn’t understand why that was a thing. Anyways that’s a prime example of covering your tracks. You hide in plain sight. The problem with my tactic, right, was that once someone tried to use Safari they would realize that something was wrong. That red flag in their head would get thrown and that was when they read me basically alerting them that “You got trolled by young James this leet hax0r skid” (Lol throwing major shade at my younger self here, don’t dox me XD )
-
Basically do some Anti-Forensics etc. to showcase what a Black Hat (lol buzzword) would do.
-
-
Phase 5: Analysis & Report
- This is where you gather all the data, and every single thing you did above, into a massive report. You make a presentation. Report on your findings, what you did, and assess the clients overall security.
- In that mind set of a Risk Assessment.
- You would also include in your report a solution document, that would detail on how to prevent the attacks you executed from happening, and the client will have to decide to make those improvements.
- I’m not a fan, so I’m not gonna blaaahhh(firehose you with info) and say “OMG THIS IS SO COOOL” when it’s my least favorite thing, paperwork and writing reports. But this is the most important part of the entire job so it has to get done well.
- This report and documentation is the last core resource the client will get from you, as it is not your job to fix their security holes it’s up to them to take your advice or ignore it(believe it or not companies do ignore it sometimes, it’s cheaper for them to get hacked unfortunately, no joke they would rather pay the legal fees than for security infrastructure and stuff)
-
Phase 6: Clean Up Bye
-
This is the last thing where you make sure you’ve cleaned up the mess you’ve made and ensured the company is all done with you. Who knows maybe they do hire you to fix their security holes, etc.
-
You get paid etc.
-
You have to ensure there’s remediation, and that the company has your Risk Analysis and Assessment (this would mainly be your final copy of the report with everything in it. Just with closing statements from the meeting before in Phase 5.)
-
So there you have it!! By all means this is not everything in a pentest but it’s a great sum of information. There’s definitely a lot of things still, that need to be done, and that are included in the pentest lifecycle. For example, making sure you’re checking in with your POC (point of contact) in the client site every time you’re doing something. This is to make sure you’re not gonna get in trouble and to make sure that get out of jail free card is still activated, etc.
Hope y’all enjoyed that! I do enjoy discussing Pentesting and Incident Response, they’re two big things in the Cyber Security and Digital Forensics World. Thanks for letting me help you start to explore them 🙂
I put some hints to what’s on the way but for now I’ve got a Movie, Pizza, and Wings waiting on me.
Stay Safe Out There Folks! Don’t forget to follow me on Twitter using that icon below or @j3st3rjam3s I’d love to hear from ya!
“James out”
peace signs in the air