Quick Chat: VRRP & MFA
 Hey peeps! So it’s my final semester now here at college and I have my final major class. Systems Security aka SEC440. It’s a no nonsense, no handholding, no spoon feeding class where you’re given tasks that you have no idea how to do, and you have to go research and figure it out. Honestly, I hate it and love at the same time. Shoutout to the Man of the East, who both supports me and also shoots me at the same time as the professor. :rofl:
Hey peeps! So it’s my final semester now here at college and I have my final major class. Systems Security aka SEC440. It’s a no nonsense, no handholding, no spoon feeding class where you’re given tasks that you have no idea how to do, and you have to go research and figure it out. Honestly, I hate it and love at the same time. Shoutout to the Man of the East, who both supports me and also shoots me at the same time as the professor. :rofl:
Fitting it be the last class I take outta here before I enter the real world.
So in the spirit of documentation, here’s our first lab.
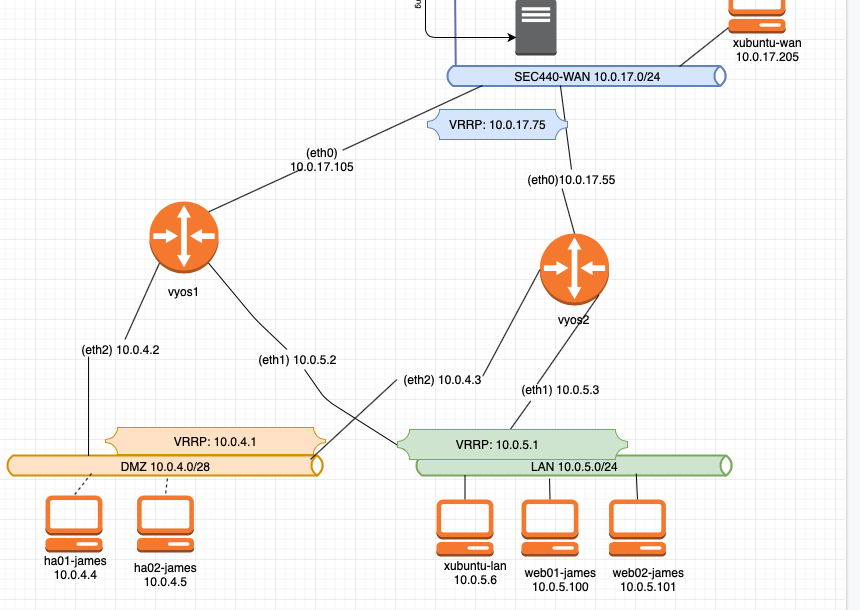
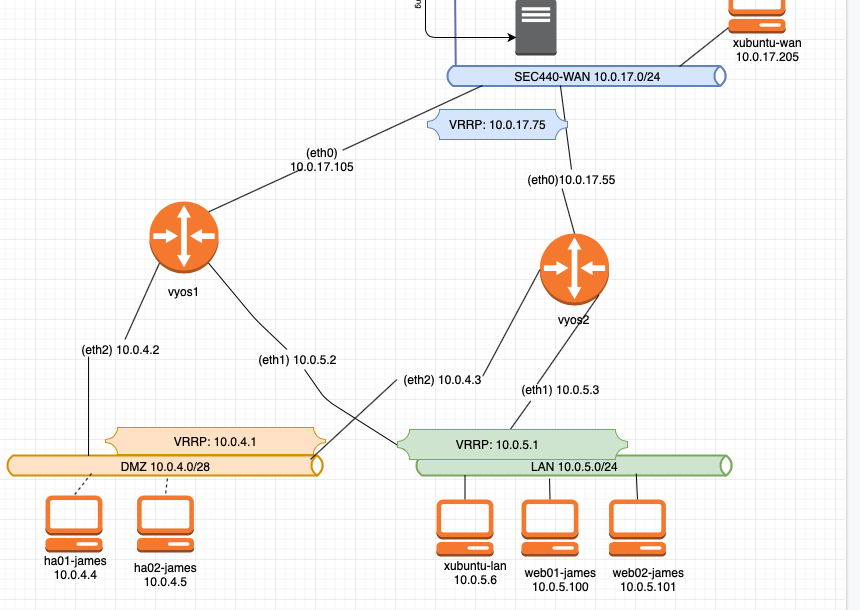
Lab 1: Router Redundancy with VRRP
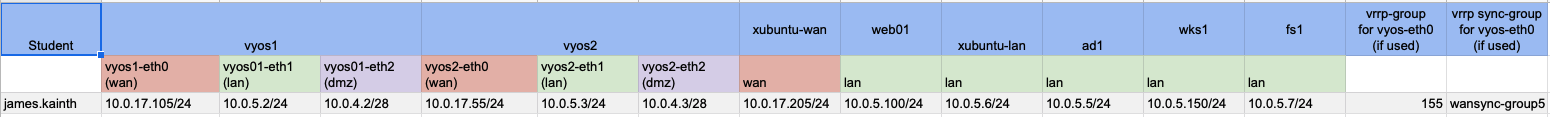
Configure and Network the following systems.
- vyos1
- vyos2
- xubuntu-wan
- xubuntu-lan
- web01
- Redundant WAN and LAN
The WAN interface on vyos1 and vyos2 should be redundant so that addressing a single IP address will route to whichever vyos router is currently active.
Your redundant WAN interface should be configured to port forward
http to web01 on the LAN.
ssh to web01 on the LAN, this should also be augmented with MFA and root SSH disabled.
Your LAN based systems should also have a redundant default gateway of 10.0.5.1 where either of the two routers providing gateway services can be taken offline without an interruption in service.
Needless to say it’s pretty easy with the assist of my command-center. Port forwarding means using NAT rules. Obviously set name server, gateway, assign interfaces, etc. But the new thing is VRRP.
What Is VRRP
VRRP is a network protocol that provides that allows multiple routers/hosts to share an IP. This increases the availability and reliability of routing paths via automatic default gateway selections on an IP subnetwork.
Thankfully for VyOS setting it up is very simple.
Here Are The VRRP Commands:
configedit interfaces ethernet [eth#] vrrp vrrp-group [# that’s assigned to you]set virtual-address 10.0.17.77set preempt trueset priority [#]set sync-group [name assigned]commit
So you must execute those above commands on two routers that will be redundant. Make sure you set the priority of one router to be higher, for failover. Next make sure the virtual address, vrrp-group, and sync group, are the ones that are assigned to you. You don’t want to steal someone’s IP address and cause hysteria.
What Is MFA?
MFA a.k.a. Multi-Factor Authentication is exactly what it sounds like just another factor that you can implement for added security. In this lab I’m going to be using Google Authenticator.
Setting Up MFA:
yum install -y https://dl.fedoraproject.org/pub/epel/epel-release-latest-7.noarch.rpmyum install -y google-authenticatorgoogle-authenticatorecho “auth required pam_google_authenticator.so” >> /etc/pam.d/sshdsed -i ‘s/ChallengeResponseAuthentication no/ChallengeResponseAuthentication yes/g’ /etc/ssh/sshd_configsystemctl restart sshd
And that’s it!
Hope you found this quick chat a lil useful! Hopefully soon I’ll post a Let’s talk about, I just need to get my footing now that we’re in the Endgame now.
That’s right. This time. It’s my turn 😉